From Image Chaos to Control: How AVM Brings Automation and Lineage to Container Security
If you are on a release management or DevOps team, you already know the sinking feeling of a new CVE dropping.
A CVE (Common Vulnerabilities and Exposures) isn't just a bug; it is a publicly disclosed security flaw that serves as a beacon for attackers. When a critical vulnerability is announced, one that allows complete system compromise the clock immediately starts ticking.
For our team, this pressure was compounded by scale. Our organization manages infrastructure for 50+ Enterprise clients, each with unique constraints on the container image versions they allow. These clients expect images with zero or minimal vulnerabilities, making pre-deployment scanning critical for trust and compliance.
When a CVE hit, we didn't just face a coding problem, we faced a massive workflow problem.
The "Scattered" Workflow Problem
Before we revamped our approach, the vulnerability management process looked something like this:
- The Triage: The release management team pulls a massive list to see which releases are where, and what vulnerabilities exist. They segregate this list and hand it out to various development teams.
- The Investigation: Individual teams look at their assigned images and CVEs to figure out the fix, some require code changes, others just need base image updates.
- The Hopscotch: Developers navigate to their registry (like AWS ECR) to pull the image, switch to a separate scanner tool to run a scan, and then hop back to their local environment to analyze the results.
- The Loop: After applying a fix, they push the image back to the registry, trigger another manual scan, and hope it passes.
This entire process was scattered. It required constant context-switching across different URLs and tools, making manual scanning and tracking across multiple image versions time-consuming, error-prone, and inefficient.
We realized that adding more manual security checks wouldn’t fix this. The problem wasn’t our engineers, it was the lack of centralized visibility and automation, which inevitably led to delays, security risks, and operational overhead.
The Solution: Agentic Vulnerability Management (AVM)
To fix this, we built AVM (Agentic Vulnerability Management).
AVM is an enterprise-grade solution designed to centralize and streamline the management of container images across your organization. It serves as a single source of truth for all container images used in your organization, enabling teams to discover, track, scan, remediate, and govern container images throughout their entire lifecycle.
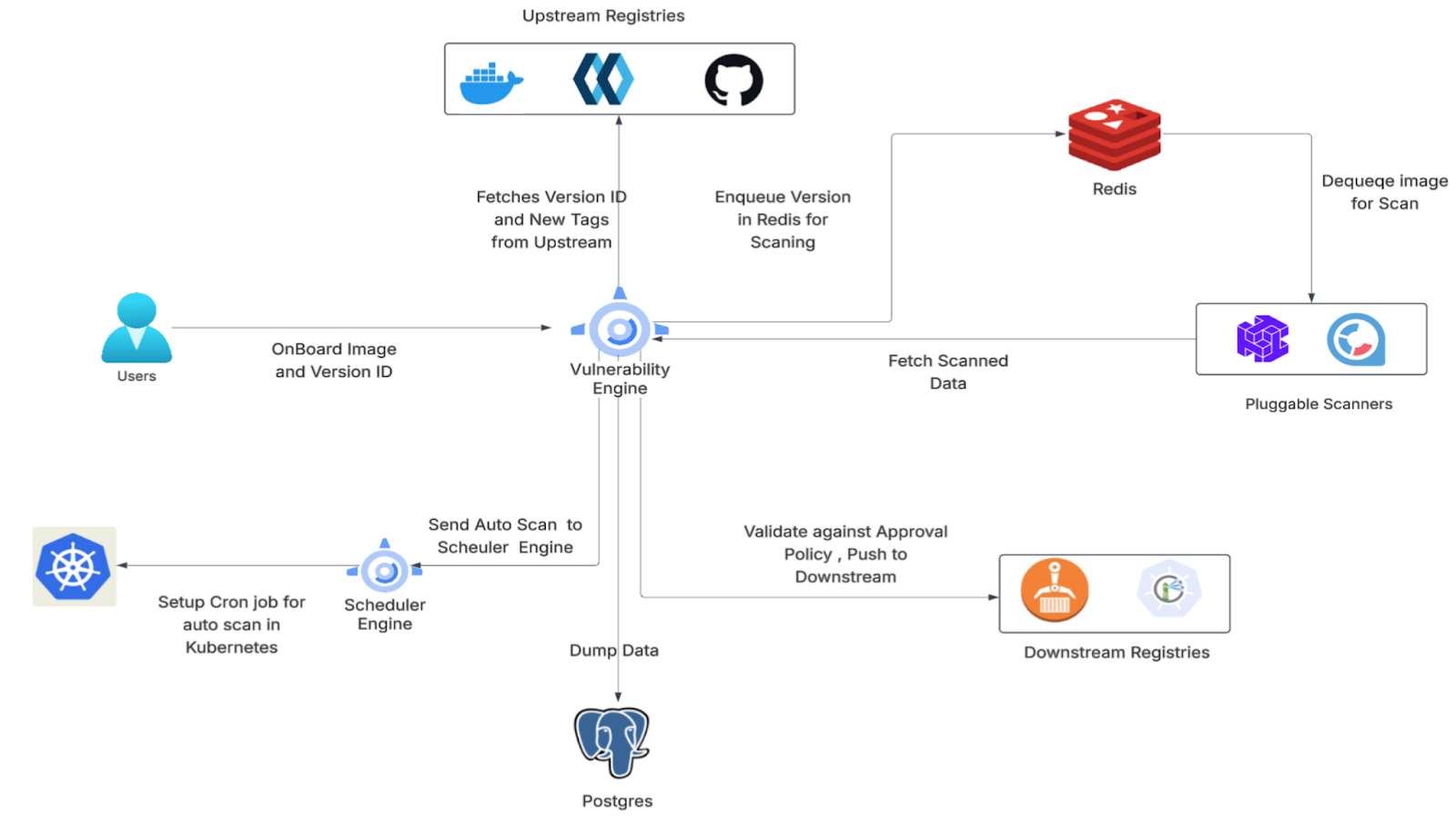
Instead of hopping between tools, AVM sits in the middle as the orchestration engine:
By centralizing the entire process, AVM gives teams a unified, single pane of glass to monitor build and vulnerability history across their entire image catalog:
Moving from Tags to True Lineage
Old vulnerability tools just look at strings of tags. To build a truly reliable catalog, AVM introduces a structured hierarchy to bring order to the chaos:

Categories include the following types:
- Foundation Images: These are the images that are used as reference inputs and are not actively managed within the platform.
- Managed Images: These are the images whose lifecycle is actively tracked and influenced by the platform.
Instead of a chaotic list of raw assets, AVM organizes these into logical, easily navigable Image Groups in each category:
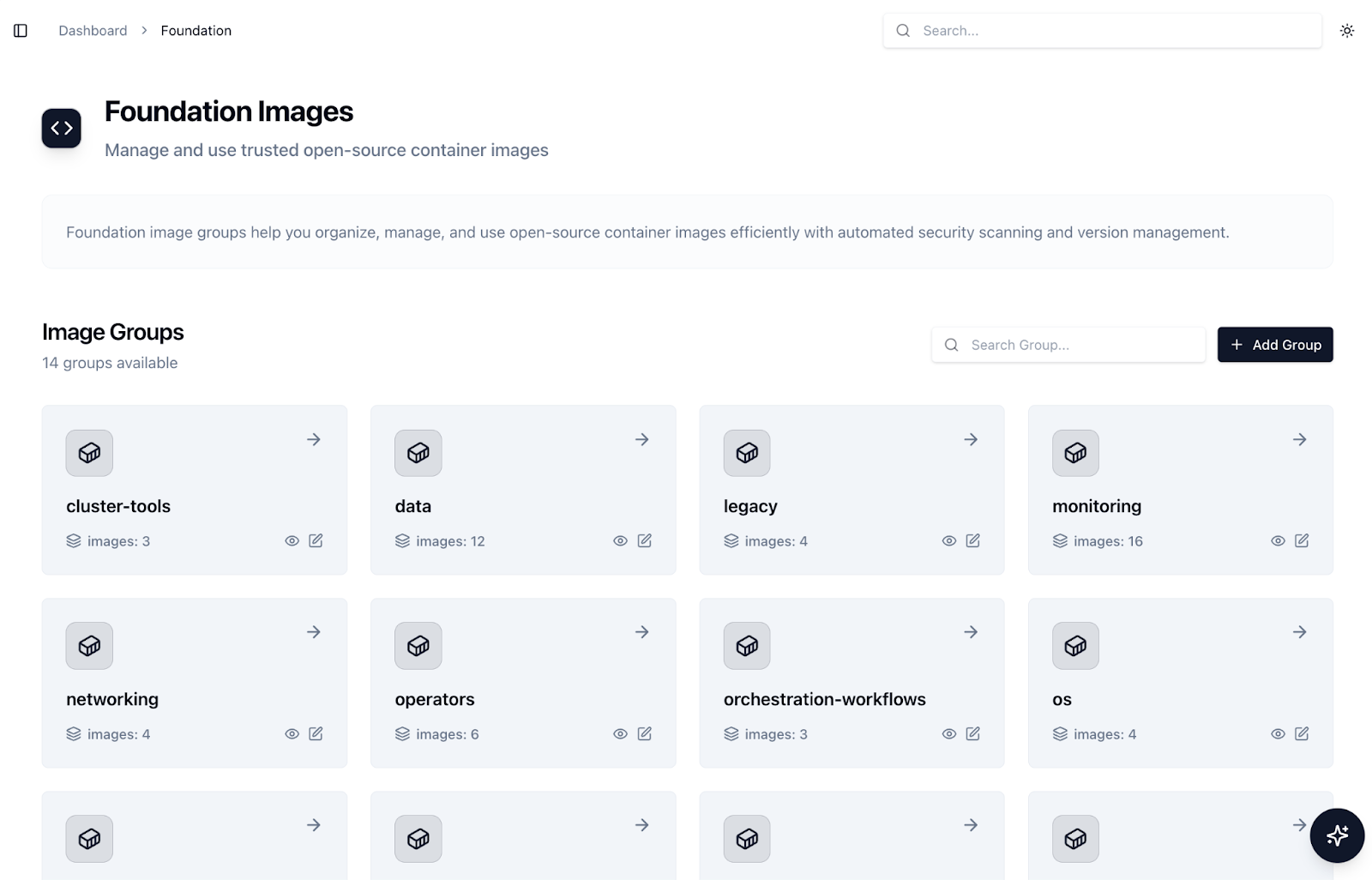
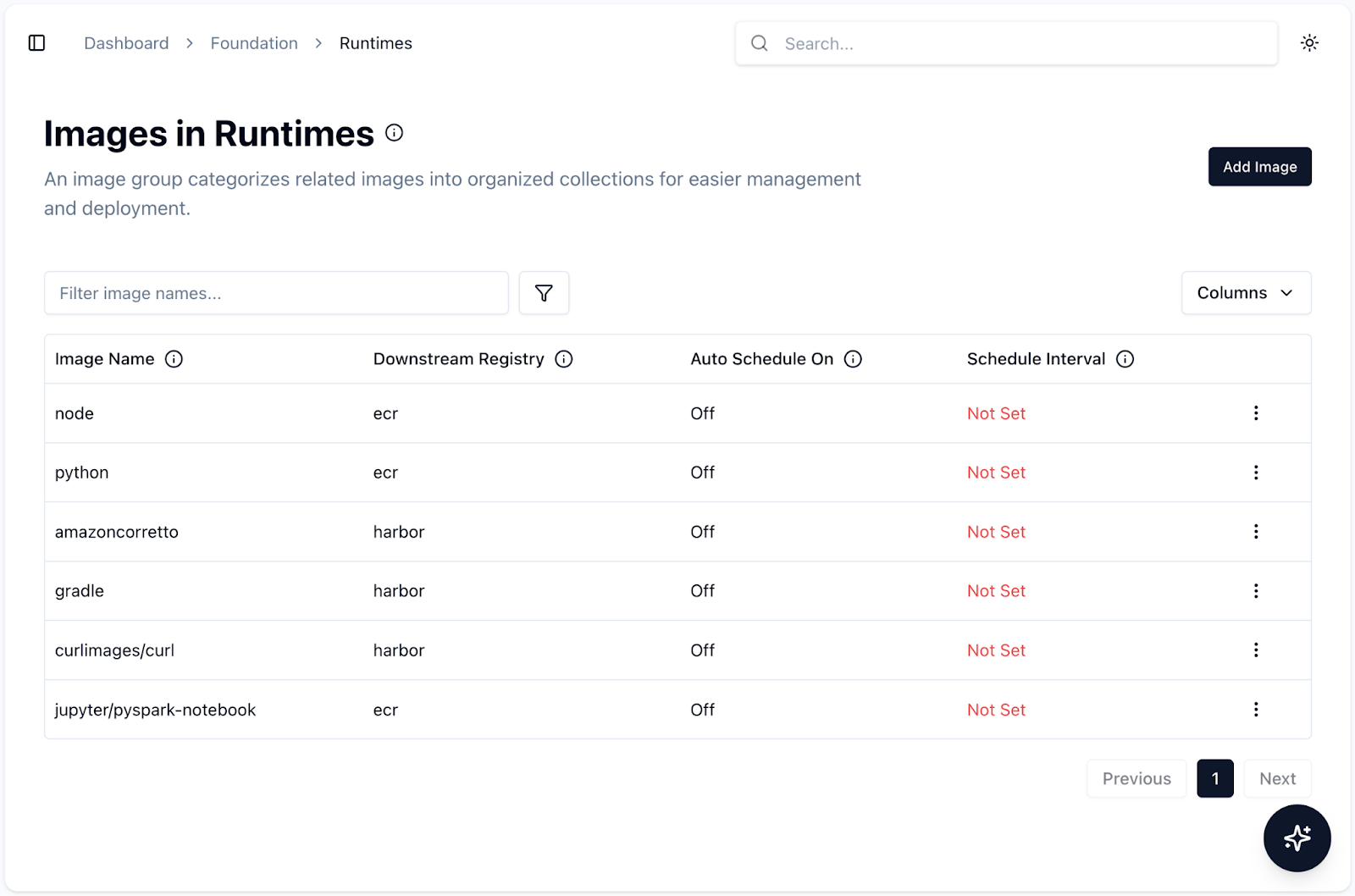
Drilling into any of these groups reveals the specific images being tracked, along with their target downstream registries and automated scan schedules and other metadata:
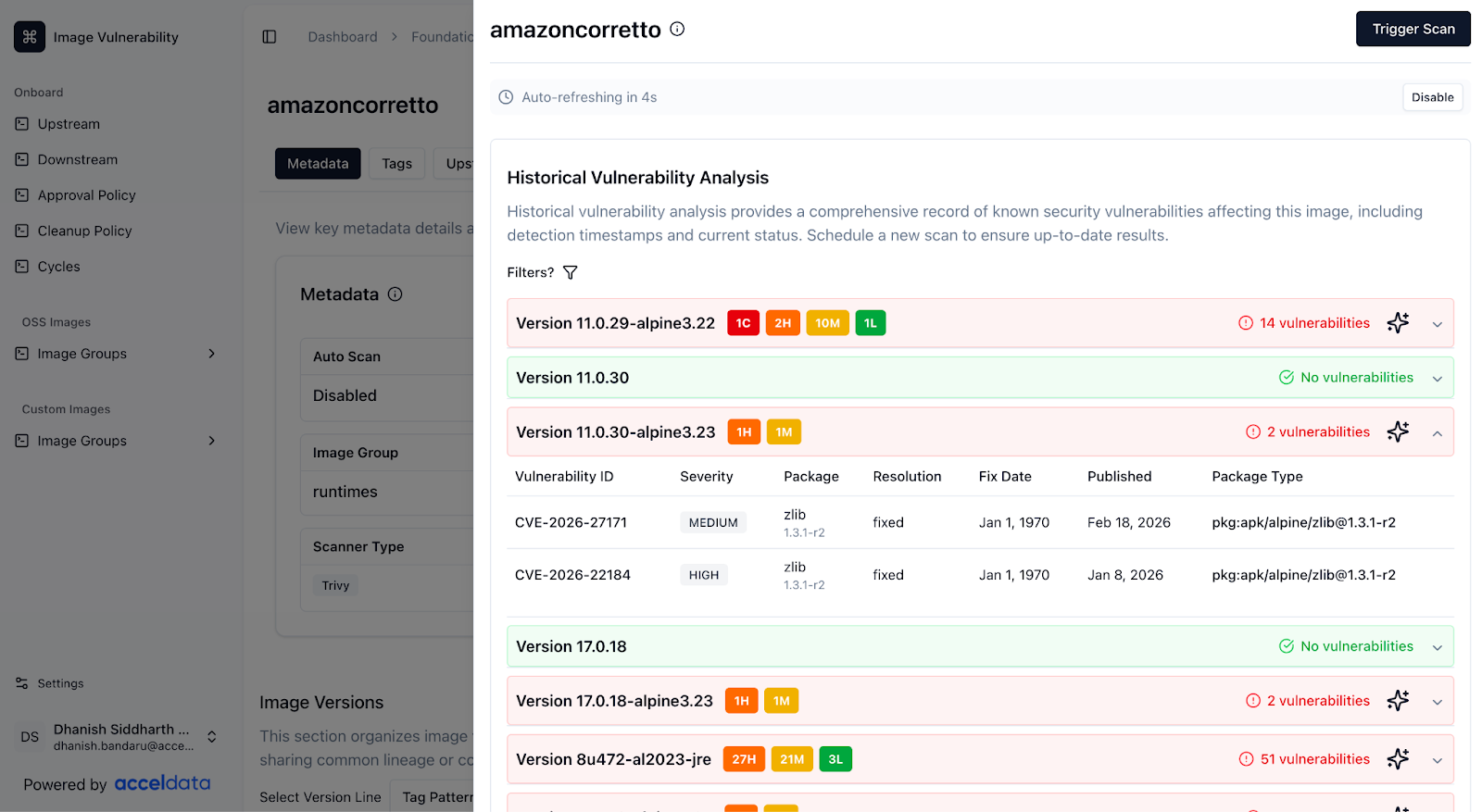
Clicking into a specific image, like amazoncorretto brings order to the chaos, providing a centralized catalog for monitoring all build and vulnerability history:
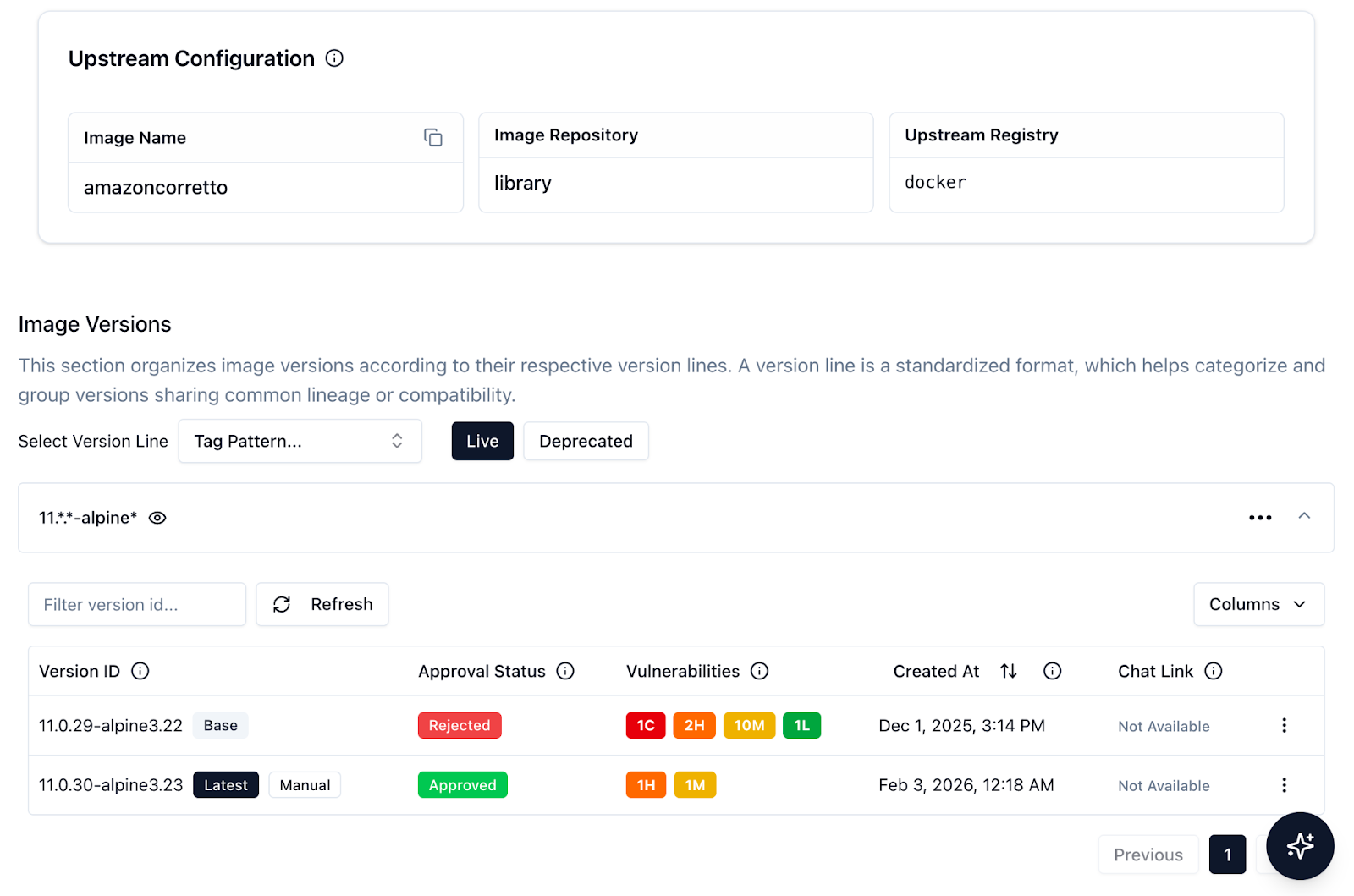
The real magic happens at the Version Line level. For Managed Images, AVM doesn't just track tags, it represents a specific parent image, a specific parent version line, and a specific build context or build approach. Because AVM knows exactly where an image came from and how it was built, we can associate a set of Policies(that help users certify images/tags) right at the Version Line level.
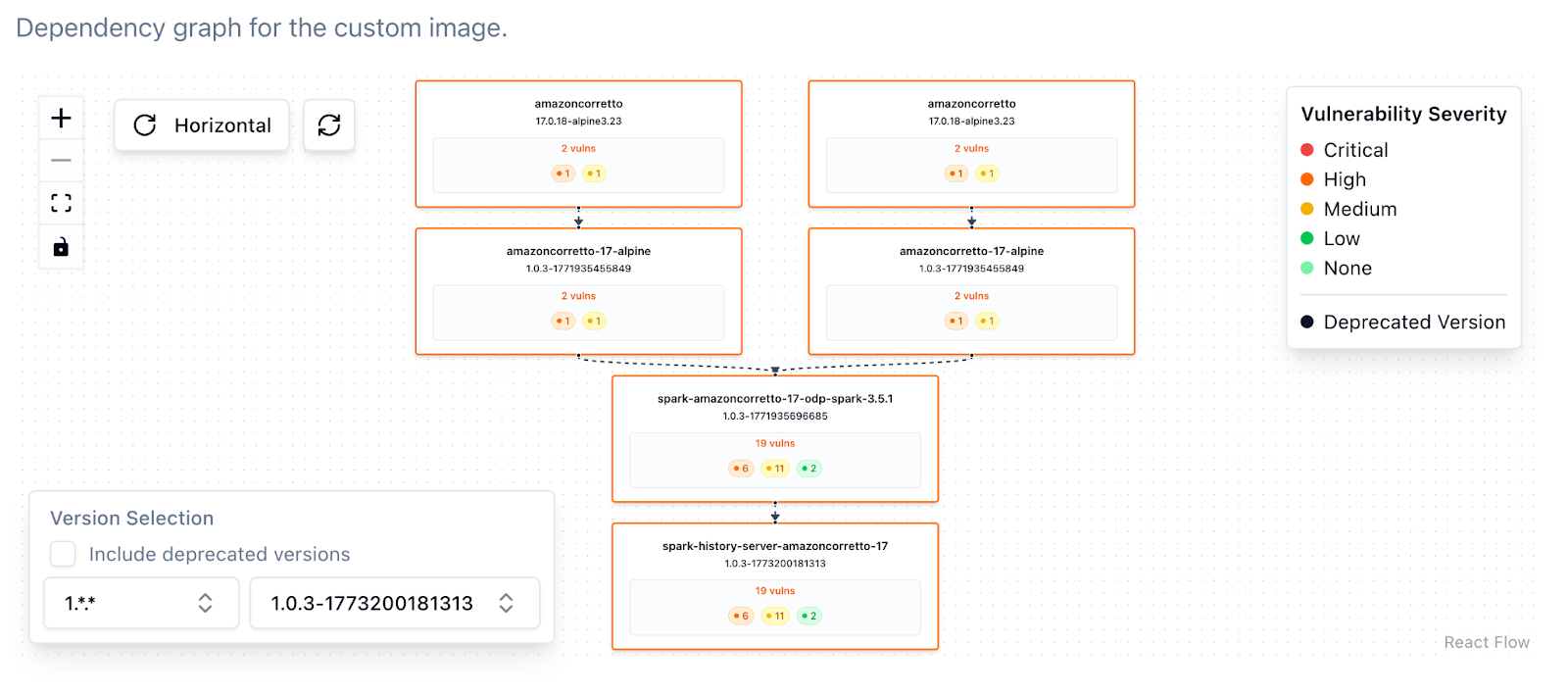
This gives us complete, visual traceability of how a vulnerability in a base image trickles down to a custom application:
A Deep Dive into Vulnerability Management
This lineage tracking is not just cosmetic; it drives a massive jump in remediation speed. AVM goes deep, visualizing complex vulnerability dependency trees and offering actionable remediation context. It doesn't just list CVEs; it prioritizes them and presents the fixes right alongside the vulnerable image.
The "Set and Forget" Reality: Continuous Monitoring
Before AVM, finding new vulnerabilities meant relying on a developer remembering to manually trigger a scan. But vulnerability databases update constantly; an image that is perfectly safe today might be critically vulnerable tomorrow.
To solve this, we built Cycles, scheduled jobs that automatically trigger vulnerability scans for specified images at defined intervals. Once an image or Version Line is set up, AVM takes over. The platform automatically creates a Kubernetes CronJob behind the scenes that triggers scans and fixes at calculated times.
This ensures continuous monitoring of image security posture without manual intervention. If a zero-day CVE is disclosed overnight, AVM catches it during the next automated cycle, immediately re-evaluates the image against your strict Policies that the user sets in AVM to certify images, and flags it. No manual scan triggering is required. You simply set the schedule, and the system ensures you are never caught off guard.
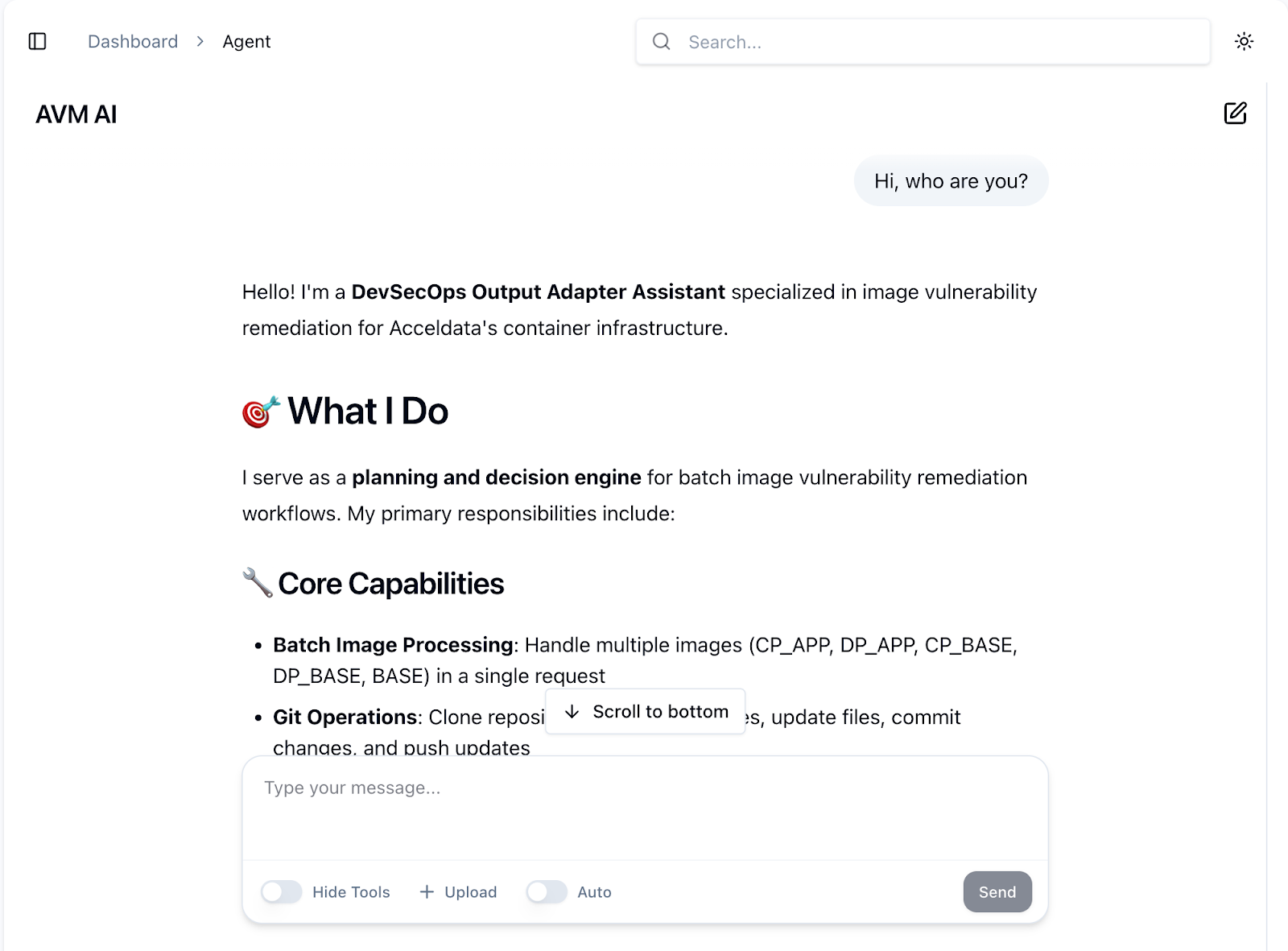
The AI Agent: From Passive Alarms to Active Fixes
Centralizing the catalog and automating the monitoring was step one. Step two was making it Agentic.
Vulnerability tools usually just point out what's broken and leave you to fix it. AVM utilizes AI-driven workflows, powered by our advanced LangGraph-Based agent to actively resolve the issues it finds.
When an image is flagged, the AVM agent goes to work:
- It analyzes the vulnerabilities and automatically identifies fixes.
- It makes the necessary intelligent code changes, like updating the Dockerfiles/Gradle files directly.
- It automatically rebuilds images and validates the fixes.
- Once validated the corresponding pull requests are raised and corresponding notifications are sent
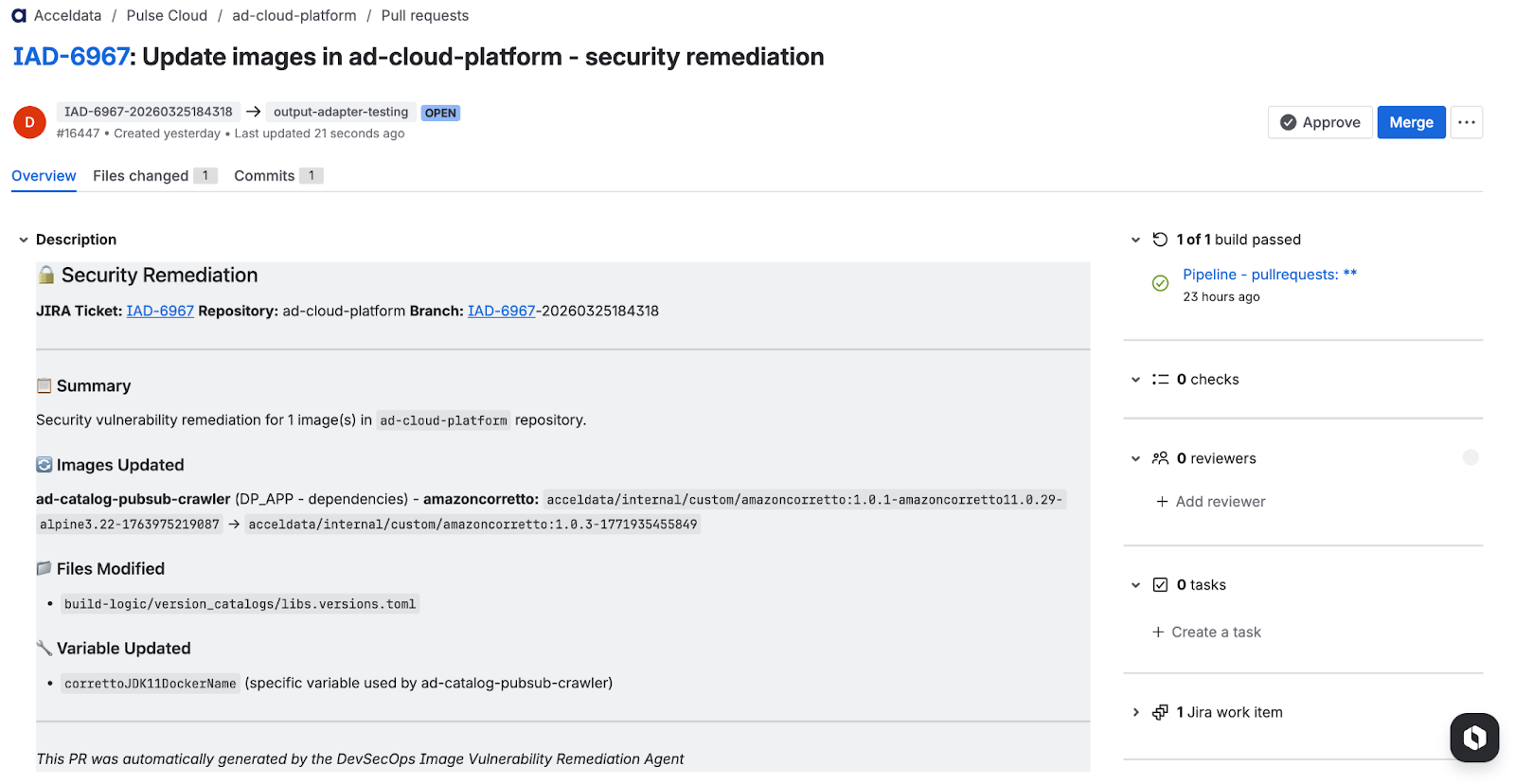
Under the Hood: What the Agent Actually Did: To understand the power of this automation, look at exactly what the agent accomplished in the PR above. The agent first analyzed the image lineage for ad-catalog-pubsub-crawler and identified that it depends on the acceldata/internal/custom/amazoncorretto image (a Java-11 base).
Once identified, the agent:
- Found the least vulnerable, compatible version of amazoncorretto.
- Cloned the repository and created a new branch.
- Made the precise code updates, specifically targeting the correttoJDK11DockerName variable in the libs.versions.toml file.
- Raised the Pull Request and attached it to the corresponding Jira ticket (IAD-6967).
Now, all that is left for the developer to do is let the CI pipeline test the new branch, click "Approve," and merge the PR.
The Shift That Actually Matters
We knew this conceptual shift was powerful, but the real-world impact became obvious immediately. By moving from a scattered, manual model to the AVM model, we completely transformed our release cycles:
- Accelerated Releases: What used to be a multi-day slog of manual scanning, triage, and patching has been drastically reduced. In many cases, releases that used to take over a week are now completed in less than a day.
- Massive Scale: We went from manually fixing a limited handful of vulnerabilities per cycle to automatically resolving hundreds of CVEs across our Managed Images.
- Engineer Efficiency: Instead of playing hopscotch between AWS, standalone scanners, and local environments, our engineers are back to doing what they do best: building features. Their output has skyrocketed because the AVM agent handles the heavy lifting.
Check out this informative video from the Acceldata DevOps team to get a clear overview of agentic automation for detecting, understanding, and remediating image vulnerabilities:
AVM: Automation to Detect, Understand, and Remediate Image Vulnerabilities
Every enterprise scaling its cloud infrastructure eventually learns this lesson: Security without automation is just delayed vulnerability.
AVM shifts the paradigm from finding vulnerabilities to managing them agentically and efficiently. By centralizing the image catalog, tracking true build lineage, setting up continuous monitoring cycles, and deploying AI to handle the remediation heavy lifting, we’ve removed the scattered chaos of release cycles.
Now, when a CVE drops, it doesn't trigger a company-wide fire drill. It triggers an agent.